If your company is a U.S. Government supplier, contractor or sub-contractor — especially one working through the Department of Defense — expect a cybersecurity inspector to visit soon.
The reason? Uncle Sam demands protection against unauthorized access to Controlled Unclassified Information (CUI). And he has given ample time and warning to contractors to fully secure their computer networks.
The DoD calls this proof of CUI security NIST 800-171 Compliance Documentation. It is required to meet the Defense Federal Acquisition Regulation Supplement (DFARS) minimum security standards.
These NIST cybersecurity requirements were first outlined in 2016 to keep the DoD supply chain networks clean. Back then, the DoD offered many helpful suggestions and asked nicely for compliance and documentation.
But in the summer of 2019, the tone of their ask changed. DoD lawyers made it clear that the documentation confirming network cybersecurity measures must be readily available for audit. At any time. Upon demand.
Recently, DoD inspectors began showing up unannounced at government and military contractors’ offices to review the required cybersecurity compliance records. Don’t have the NIST 800-171 documentation ready? The result can be a worst-case scenario: a BLACKLIST. Sorry, no more government contracts.
A Simple, Affordable Pathway to NIST Compliance
If you’ve reviewed the requirements related to NIST (National Institute of Standards and Technology) compliance, it can make your head spin. Read it for yourself here. Scores of highly technical documents that must be written using an instruction set that is a challenge to read, comprehend, and act upon. Even experienced IT professionals can struggle.
The solution? A step-by-step software package available to create all of the required NIST 800-171 documentation. That software is called CyberConfirm™
A partnership between a nationally-known, highly-accredited, military-focused cybersecurity expert and the country’s premier pro se legal document software company led to the development of CyberConfirm. Together they have built an easy-to-use, affordable, future-proofed solution.
LEARN MORE: About Us >
Easy-to-Use Software, Step-by-Step Simple
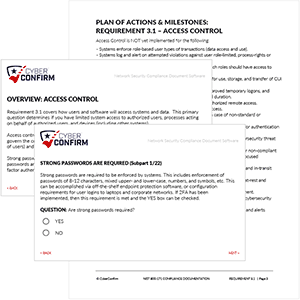
CyberConfirm™ is a downloadable document software product that is fully-secure, PDF based, and completed offline following step-by-step instructions.
Answer a series of questions about your organization, your network, and its set-up. The files generate the required NIST 800-171 compliance documents (SSP and POA&M) based on your answers, all customized to the current security status of your business.
The document-creation process has been further simplified by narrowing the 14 Requirements into a series of 110 numbered control components. Start and stop as often as needed. Tackle one compliance Requirement at a time. When finished, put all of the completed Requirement sections together for a document set that is ready for the day when the DoD comes knocking.
The finished compliance documents are provided in PDF format, ready-to-print. The document pages are output with a clean, professional design. The report’s cover page is fully-customized to feature your company name and logo.
Expect to make future changes to your cyber network? Simply update the answer(s) in the Q&A process, print out the revised document section(s), and recompile the finished document package. Easy!
LEARN MORE: How CyberConfirm Works >
PREPARE FOR CMMC: the NIST 800-171 requirements will roll into Cybersecurity Maturity Model Certification (CMMC). Fully aware that change is constant, CyberConfirm software is built in preparation for those future requirements: no time or effort is wasted! Use the answers from the previously-completed 171 documentation to create the new CMMC documents when the time comes. CyberConfirm is NIST-compliant today, allowing users to work toward CMMC-compliance in the future! CMMC Rollout Updates >
Required for the Networks of All DoD Contractors & Subs
If your company has not yet created the DoD-required NIST 800-171 Compliance Documentation for your corporate network, your livelihood is in jeopardy.
Any government or military contractor or sub-contractor that cannot produce its network security documentation upon demand can be removed from the list of authorized DoD suppliers. That means no more government contracts for your company. Period.
But there is one important caveat to the government’s demand.
A contractor need not prove full COMPLIANCE with all NIST 800-171 standards for their network. Not yet.
Rather, the contractor must provide completed DOCUMENTATION while working to meet the NIST network standards.
Understand? As long as a company is working toward implementing the required security measures and fully documents the process while doing so, the DoD won’t bring the hammer down on that contractor.
In essence, the completed NIST 800-171 documentation is like having a ‘Get Out of Jail FREE’ card!
So keep the DoD at bay: create your compliance documents today! Get CyberConfirm™.
LEARN MORE: Is CyberConfirm Right For You? >
Use the Language of a Cyber Security Expert!
If you review the long, detailed instructions covering each requirement for NIST 800-171 documentation, you will immediately notice something missing: each requirement is discussed in great detail, but that discussion never provides (nor even suggests) the language that should be used in writing your own network documentation.
In essence, NIST provides an outline of topics that need to be covered, but leaves it up to the network’s owner to draft the language. Unless you are a highly-experienced cybersecurity expert — well, good luck with that.
But what if you had access to the mind of a nationally-recognized cybersecurity expert? One who frequently sits in on meetings with DoD brass talking cyber? Who has drafted this type of documentation many, many times over his 30+ year career, for clients big and small?
Bet if that cybersecurity expert provided the wording acceptable to the DoD based on the security status of a company, that kind of help would go a long way.
Yes! Of course it would! And that’s exactly the type of knowledge you get with CyberConfirm™.
Get DFARS Compliant While Creating Your Cybersecurity Plan
To be clear: there is more to NIST compliance than just creating documentation. There are a number of physical actions that must be completed to become fully compliant with NIST 800-171.
Smartly, each of these critical security actions is discussed as part of the step-by-step document creation process.
With each Requirement overview, you will be given clear instructions on hardware and software specifications that must be implemented over time to fully secure your cyber network.
As you work through the documentation sections, you will be made aware of actions that must be taken specific to that particular Requirement.
And should you need hands-on help in fully securing your network or addressing other critical needs, contact information for professionals in our PRO cybersecurity consultants network is available.
But the Price is So Much Lower?!
Why is CyberConfirm so much more affordable than other competing solutions? That’s a great question. Likely, the answer says more about the values of our competitors than the value of our software product.
Our software is complete and comprehensive. It is authored and compiled by industry leaders. We set a price that fairly compensates us for the knowledge, time and work involved, both for the initial purchase and for future annual renewals.
So if our competitor is charging significantly more than we do here at CyberConfirm, why that is becomes more a question for the competitor than for us…
Need more information before purchase?
Check out our FREQUENTLY ASKED QUESTIONS section. Or send us an email asking any questions you may have!
The standard version of CyberConfirm™ is licensed for a single end-user of the documentation software. For software licensed for a consultant or managed service provider on behalf of multiple clients, see the CyberConsultant PRO Package >